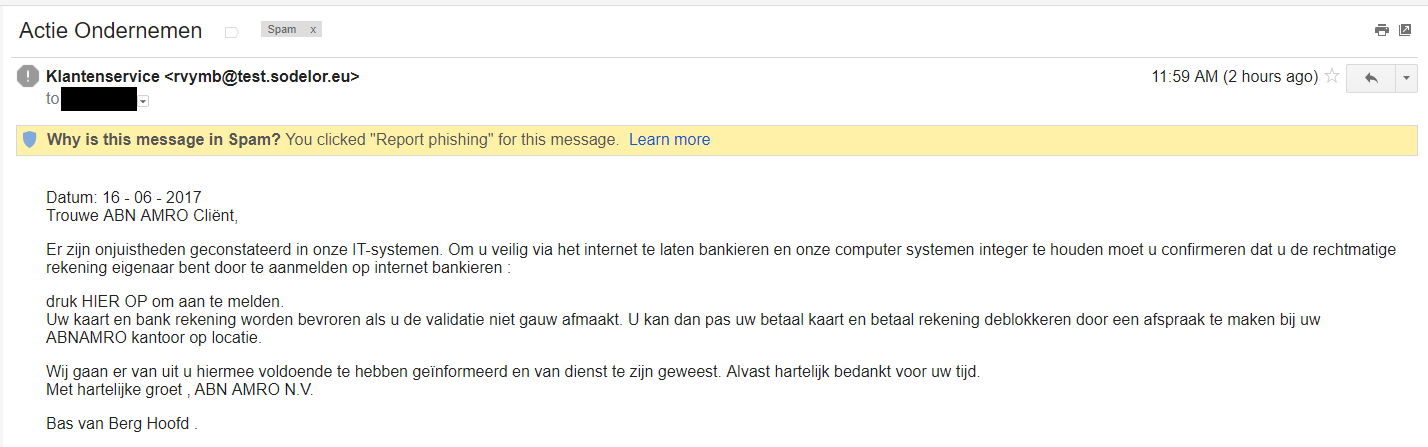
It’s always interesting to see a bank like the Rabo warning me about the possible dangers of their systems by using emails like these. It’s even more interesting when you realise that I don’t have a Rabo account thus there’s no reason for me to use their software. So, yeah… It’s a phishing email, but for GMail it’s still a reasonable new attack so I don’t get an automated warning. (McAfee did detect a potential unsafe link, so that’s a second warning.)
It’s always interesting to see a bank like the Rabo warning me about the possible dangers of their systems by using emails like these. It’s even more interesting when you realise that I don’t have a Rabo account thus there’s no reason for me to use their software. So, yeah… It’s a phishing email, but for GMail it’s still a reasonable new attack so I don’t get an automated warning. (McAfee did detect a potential unsafe link, so that’s a second warning.)
Roughly translated, the message is telling me the bank is using a new security system which is supposed to keep me safe from any malicious software. All I have to do is link my system to theirs, offer some more information and then I won’t have to worry about my bank account. (Probably because they will plunder it to the last penny.) After providing my information, they will contact me by phone and update my account so they can collect even more sensitive data from me.
Well, this is a nice example of a phishing email. First of all, my bank should already know all information about me that they need. If not, I should receive a link to their official website with the proper logo’s and stuff, plus a secure SSL connection. By providing a “special link” that would allow me to add my information, they’re actually making me more suspicious. Normally, a bank would tell you to log in to the regular website and then select option X from the list of options to give more information.
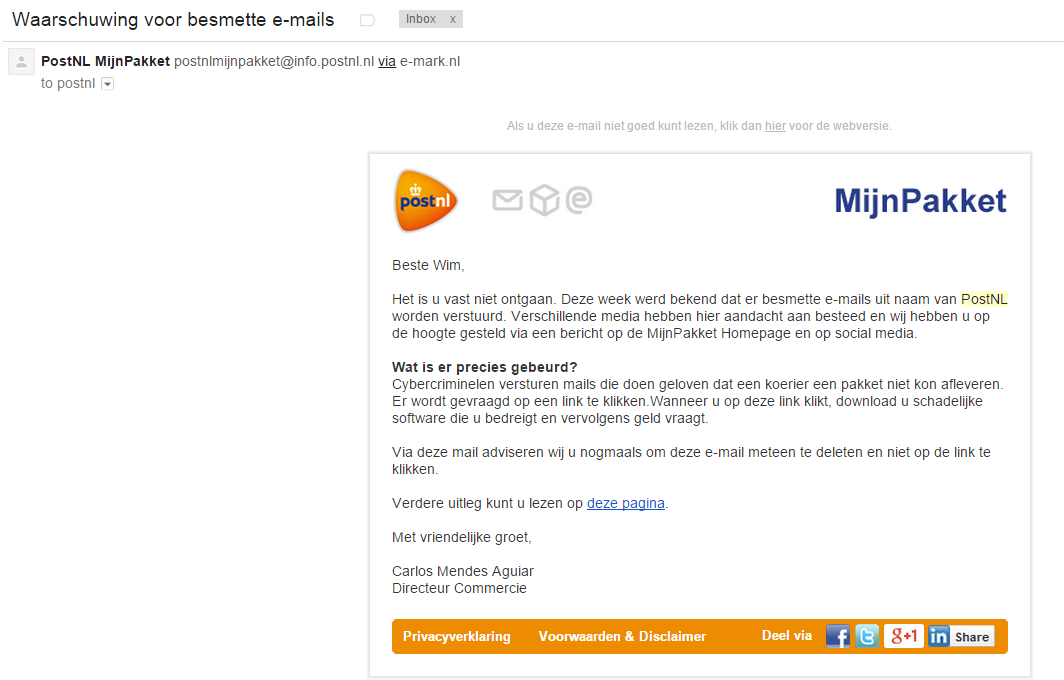
Also, since modern banks will handle almost all client interactions through secure webpages, there should never be a need to install software that your bank provides! I even become suspicious when the ING started to offer an extra malware checker to all their customers, because even though this was a legit offer, it encourages people to install anything the bank tells them. This is bad, real bad! So, to all banks: please stop telling us which software we need to install and where to download it.
Basically, the mail is telling me to do things no ‘real’ bank would even ask of me. (If they did, I’d leave them for another bank.) But they’ve also sent this email to someone with no Rabo account, which is plain stupid since those people should recognise this as spam immediately and thus report it immediately. Gmail, for example, has a nice feature allowing you to mark the email as a phishing attempt. If a few people report this as phishing, it will be automatically sent to the spam folder for everyone.
But there’s more and for this I will have to look at the email header:
Received: by 10.50.78.199 with SMTP id d7csp60995igx;
Fri, 16 Aug 2013 01:08:54 -0700 (PDT)
X-Received: by 10.180.9.203 with SMTP id c11mr114146wib.64.1376640534320;
Fri, 16 Aug 2013 01:08:54 -0700 (PDT)
Return-Path: <informatie@rabo.nl>
Received: from web017.kontent.com (web017.kontent.com. [81.88.40.153])
by mx.google.com with ESMTP id vl2si80185wjc.138.1969.12.31.16.00.00;
Fri, 16 Aug 2013 01:08:54 -0700 (PDT)
Received-SPF: neutral (google.com: 81.88.40.153 is neither permitted nor denied by best guess record for domain of informatie@rabo.nl) client-ip=81.88.40.153;
Authentication-Results: mx.google.com;
spf=neutral (google.com: 81.88.40.153 is neither permitted nor denied by best guess record for domain of informatie@rabo.nl) smtp.mail=informatie@rabo.nl
Received: from 123salonmagie-pittelkow.de (localhost [127.0.0.1])
by web017.kontent.com (Postfix) with SMTP id 48F4C1906F
for <xxxxx@xxxxxxxx.xx>; Fri, 16 Aug 2013 10:08:53 +0200 (CEST)
Received: by 123salonmagie-pittelkow.de (KT-sendmail/237034); Fri, 16 Aug 2013 10:08:53 +0200
Date: Fri, 16 Aug 2013 10:08:53 +0200
X-Kontent-Script: http://123salonmagie-pittelkow.de/images/hdds/gtr/mailer1.php
X-Kontent-Sender: 41.137.57.141
To:xxxxx@xxxxxxxx.xx
Subject: 2013 Rabo Bank Algemene voorwaarden en informatie
From: Rabo Bank <informatie@rabo.nl>
Reply-To: informatie@rabo.nl
MIME-Version: 1.0
Content-Type: text/html
Content-Transfer-Encoding: 8bit
Message-Id: <20130816080853.48F4C1906F@web017.kontent.com>
One thing I immediately notice is that the email has an email address from the sender (informatie@rabo.nl) which seems suspicious valid. Most banks will have a no-reply address as sender since they don’t want their clients corresponding with them by email. Why? Because email is less secure. Thus this too is a warning signal.
The reference to ‘kontent.com’ is also suspicious. But when you visit this domain (it’s safe) you will see a domain hosting company that also provides web mail options. It tells me that the email has been sent through their servers. But the trail goes further. A german domain provider, which is strange since the Rabo is a Dutch bank. The domain registered at this provider is 123salonmagie-pittelkow.de and it seems to be down already. The WhoIs information makes it clear that the persons behind it want to be anonymous, so it’s registered by ‘Kontent’.
An IP address (41.137.57.141) is also noticeable. RobTex tells me this is an address in Morocco. An added descriptions shows “This prefix is dedicated to mobile 3G Internet users on the capital Rabat and its surroundings” which tells me someone is using a mobile phone or tablet to send these phishing emails from Rabat, Morocco.
Back to the domain I’ve found. Again, RobTex shows me it shares its site with dozens of other sites. Many of them look suspicious or are gambling or porn-related. That doesn’t really surprise me. These are all just hosted sites, with small sizes and not too many visitors. An ideal provider for a phishing attack. Especially since this provider allows their customers to send emails from a domain name (rabo.nl) that doesn’t belong to them.
The phishing attack is done in a smart way. Since the frauds are working on an international level, the risk of getting caught is reasonable small. They do seem to understand the Dutch and German language, but then again, these two countries have a lot of immigrants from Morocco. The fraud might even be in Morocco for a holiday, returning in a few weeks and thus removing his traces in Rabat.
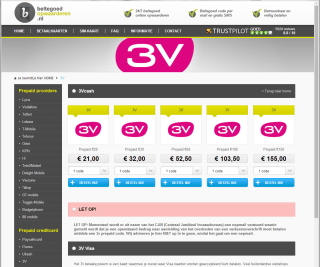
To pay the provider, he probably used a hacked bank account or credit card. In Rabat, he could have stolen an iPad with 3G connection and used that to send the emails. On his domain name he probably used a simple script allowing him to send a huge amount of emails through the provider without warning bells going off. Then again, similar Rabo phishing emails are going around for two years already, with just a few minor changes. This fraud is probably doing this for a while now. It tells me that he has escaped being captured for quite a while.
But would he really profit from this? Well, the risks are small since he misuses systems in two different continents and is probably using fake names and stolen bank information to get the things he needs. With about 15 million people in the Netherlands, he might just mail 10% of them, hoping that 1% of those will click the link and offer at least some information. If 1% of this information is valid, he will have collected 150 valid bank accounts. If he can “steal” 500 euro’s from each of these accounts, he will have earned 75.000 euro’s, which happens to be a very nice amount. If he can keep 10% of this amount and spend the rest on expenses, it would still keep him well-paid for two months. Longer if he lives in Morocco.
Basically, people who fall for this fraud will be sponsoring some criminal in Morocco. When you realise that several muslim-extremists have ties with Morocco then this kind of fraud might even be sponsoring terrorism. Thus it’s very important that people are very careful with these kinds of emails. And even more important: never communicate with your bank by email, since it’s unsafe. You can use their website, if it uses SSL. Otherwise, use the phone to call the bank when you receive emails like this and ask them what to do. Don’t use the phone number from the email but from your bank statements or from their official website. Also, keep in mind that no sane bank will ask you to install any specific product, nor should they offer you an email address for your replies. If a bank does do these stupid things, complain to them! Switch banks if you have to, since those banks are taking too many risks.