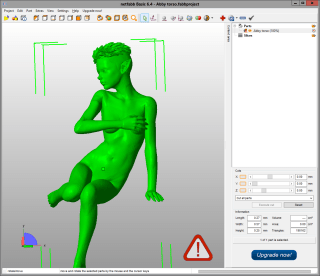
In my previous post I mentioned that I need a ruler to use with my Poser models. The reason for this is very simple. When you export a model from Poser, the proper size of the model isn’t written correctly in the export file. Poser is a great application but it has troubles doing a proper export. As a result, you might think your model is 20 cm high but it happens to be just one millimeter. Why? Because Poser doesn’t write proper measurements.
Now, things are simple when you know what size your model is supposed to be. If you want your model to be 20 cm high then you just rescale it in MeshMixer and you’re done. However, if you have a box or case as part of your project, chances are that the model will be bigger in all directions than this box. The box might be 5 cm high but the model is 20 cm high. How to fix that problem?
Well, the solution is simple. Create a model of a ruler with tags for centimeters and millimeters. Make it very long so it will be longer than your model. And when you’re modeling in Poser, use the ruler next to the object that you need to have at a precise size. Scale the ruler so the size of the object matches the desired length. Do not scale the object to fit the ruler, though! You won’t need to.
When you have set the ruler to the proper scale, you can continue to work on your model. Make the ruler about twice the length of your model, which is 60 cm for me. When you do an export, keep the ruler part of the model but move it to the side or back so it can be cut away with MeshMixer or NetFabb. This will allow you to set the proper scale in MeshMixer to 60 cm as the height (or width, depth) of your model.
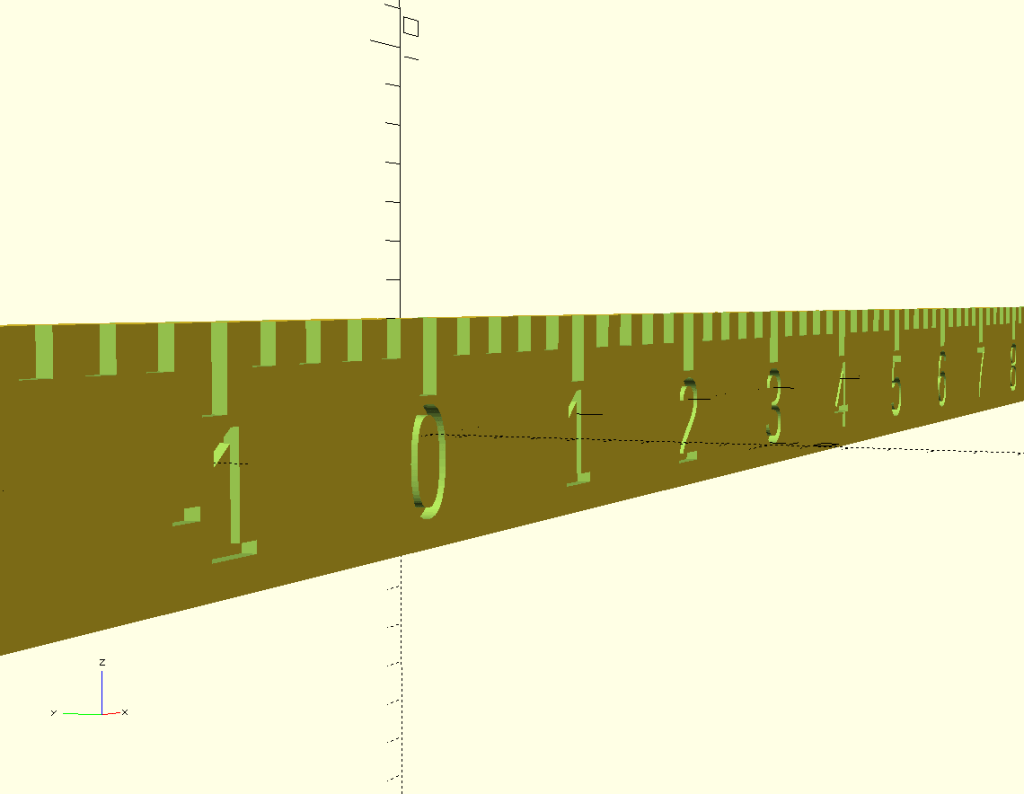
I want a simple ruler with small tags for millimeters and longer tags for centimeters. I also want the numbers for centimeters to be on the ruler so I don’t have to count. And I will number all the centimeter ticks too, just because I can.
$fn = 50;
length=300;
width=6;
thickness=1.6;
center=0.8;
module SetTag(number){
linear_extrude(height = thickness) {
text(number,
size = width/2,
font = "Lucida Console Regular",
halign = "center",
valign = "center"
);
};
} // SetTag
cube([length*2, center, width], center=true);
difference(){
cube([length*2, thickness, width], center=true);
union(){
for(i=[-length:2:length]){
translate([i, 0, (width-1)/2]) cube([1, thickness, 1], center=true);
} // for
for(i=[-length:10:length]){
translate([i, 0, (width-2)/2]) cube([1, thickness, 2], center=true);
} // for
for(i=[-length+10:10:length-10]){
translate([i, 0, -(width/8)])
union(){
rotate([90, 0, 0]) SetTag(str(i/10));
rotate([90, 0, 180]) SetTag(str(i/10));
} // union
} // for
} // union
} // differenceI created a special module to place the text on the ruler. I generally copy and paste it from my other projects since it defines my default settings for handling texts. You don’t need to do this but it makes the call to the text function easier.
I create two cubes for the ruler. One happens to be a thin part which makes the whole ruler solid. The other fattens the ruler so I can carve the ticks in the ruler without making parts too thin. This would allow me to even print my ruler, if I want to.
I’ve set up several variables so I can make as many rulers as I like, although the rendering can be a bit slow for long rulers. There are ticks carved for every 2 mm but you have to be aware that the middle of each tick is the exact place, not the left or right side of it. The zero tick is exactly in the middle, going half a mm in both directions. Keep this in mind since the ticks at 30 and -30 will be half the size of the other ticks. When you use the ruler to measure things in Poser, measure from the zero tick, not the ends of the ruler!
The numbers are at the proper spot, with all negative numbers on one side and positive numbers on the other.
This ruler is very long but that’s the purpose of this ruler. I have uploaded it to Shapeways – Ruler and it is available there for about $7, excluding postage and taxes.
In my next post I will create the case for the thermometer.